
Before you go to read different types of malware you should know.
what is malware?
Malware is a collective term used for various Malicious Software.
Malware is intentionally designed Software to gain unauthorised access, damage, interfere with a server; any electronic device, or a network without the knowledge of the respective owner.
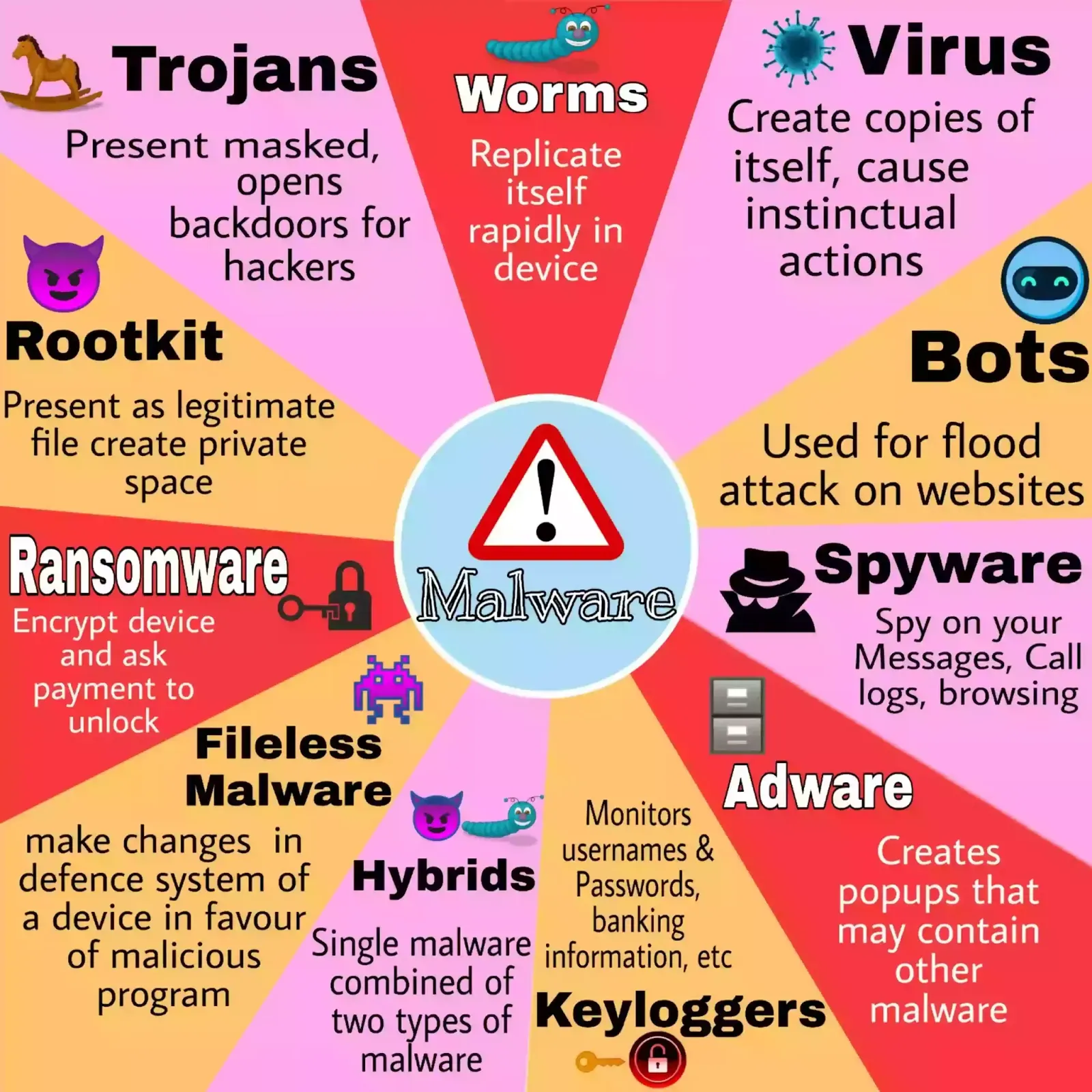 |
| Types of Malware |
11 Common Types of Malware
① Trojan horses
It is the most commonly observed Malware throughout the world which presents masked and acts as a legitimate working attractive Program. Once someone downloads that file, a Trojan finds its way into a device to create a backdoor from which hackers can release spyware or even worse which causes a leak of your personal details from your device.
② Virus
Viruses are spread from a file infected with it. When a device runs such infected files, it creates copies of itself that attach to other files present in the same device, which is why it is hard to clean the computer infected with the virus.
Once infected such device’s software may function instinctual, which let unauthorized actions occur in the device such as the automatic installation of 3rd party software, increase in software crashes, etc.
③ Worms
Unlike viruses, worms don’t need a file as a host to spread they are mostly spread with help of phishing on the internet. Which makes it the most fast-spreading and destructive Malware type.
Once infected with a particular device they replicate themselves rapidly on a device, which reduces the speed of the internet, steals personal data, deletes files, etc.
④ Spyware
Spyware is used by hackers usually to spy on you mostly for observing text messages, call logs, stealing your username and password, and many more similar things, which are hard to notice by the device owner.
One of the major concerns is that malware is not really harmful to your device but to your privacy which is the most important thing than any other thing. Fortunately, removing spyware is easy if you notice them.
⑤ Adware
Adware often referred to as ‘Grayware’ are the automatic displaying ads and popup ads that are many times not related to you.
Chances are more, the advertisements will carry you to malicious content(called Malvertising), or to a product page where if you bought something commission will be granted to the Adware’s author.
⑥ Ransomware
Ransomware may be a scary thing for many peoples as it locks your device with strong encryption and demands a payment to unlock the device where payment is mostly asked in Bitcoins to remain anonymous.
After the attack, a few days are given for the payments, if not paid user can lose his valuable data in his device.
The company with valuable data has more probability of getting such attacks as they value their data and can pay the hackers.
⑦ Bots & Botnets
Bots are automated programs that act according to command, which is mostly present on the internet.
When a server is infected with bots used to launch Bots then sever is called Botnet.
They can be used for a legitimate purpose such as ranking articles on google, increasing views on Youtube videos. On the other hand, they can be used for a malicious purpose to steal confidential data, flood the traffic to a specific server that stops the real users from connecting to a server, and many such attacks.
⑧ Rootkit
A rootkit is attached to a legitimate file, once such a program is downloaded and worked with the device system it creates a private working space for it which makes it hard to recognise many times.
Once infected it can modify your various files, browse without your knowledge, etc without the knowledge of the owner.
⑨ Fileless malware
Fileless malware when infected to a device it creates changes to the defence system in favour of the malicious program, after that this malware download other malware like spyware, keyloggers, etc
Due to untraceable behaviour, they are very hard to recognise, which makes them one of the best tools for attackers.
⑩ Keyloggers
Once infected with a device, the keylogger monitors the user’s activities such as browsing the internet, usernames & passwords, banking information, etc. which makes it one of the harmful malware for the business.
Keyloggers are spread with the help of phishing, Malvertising, and social engineering.
⑪ Hybrids
Nowadays, Hybrids are mostly used by attackers which is the combo of two types of malicious programs. For instance, if malware is combined with the Rootkit and worm, a rootkit will modify a device’s security in favour of a worm which creates working space for the worm part of the malware, making it very infectious and damaging.
Signs your device is infected with Malware
- Compared to the older device it gets slow, freezy, may crash at any time.
- Opening and closing of applications automatically.
- Unusual behaviour of Computer.
- An abrupt increase in storage.
- The automatic appearance of unknown applications
- Some text messages, emails send automatically.
- An Unrelevant popup.
- Browser’s history shows some different sites you never visited.
Preventive measures to Avoid Malware
- Keep your all applications, operating systems updated.
- Use a hard password to your various online accounts and keep changing it at least monthly.
- Don’t connect your device with an unfamiliar device or USB.
- Avoid clicking the ads which you have doubts about.
- Also, don’t use Pirated software on your devices as can cause multiple problems.
- Don’t install any app from an unknown source or unverified owner instead use the best application/ software download sites.
- Purchase premium subscription of Antimalware software such as AVG antivirus, Kaspersky Internet Security, McAfee total protection, etc.
- Don’t install applications that require too many permissions and sources from your device.
- Use a paid VPN service for using personal cellular internet as well as any WI-FI network.
- Install the firewall which is capable of detecting doubtful activities in the device.
- If found suspicious activity in the device try to find its source and type to tackle it.
- To detect malware, data mining is a very useful method available now to search the big size files.
FAQ:
❓ What harmful online programs are designed to send you advertisements mostly pop-up ads?
➤ Adware is the popup advertisements that are made in motive to harm your device or steal confidential information from your device.
have any doubts or want about other malware do ask in the comment box below, I will definitely try to answer you as early as possible.